Ecommerce security protects revenue, reputation, and customer trust when threats target your secure checkout, customer accounts, and admin access.
A store doesn’t need to be famous to be attacked—automation makes every secure online store a target.
In this guide, you’ll get PCI compliance ecommerce basics, to prevent ecommerce fraud, and customer data protection steps. You’ll also get a 30-day plan to secure an online store using SSL, MFA, WAF, backups, and malware scanning—without adding unnecessary friction to conversion.
Message Lucidly on WhatsApp for a quick ecommerce security audit and risk checklist.
What Ecommerce Security Really Covers (and what it doesn’t)
Security fails when it stays abstract. Ecommerce security is not one setting; it’s a set of choices that protect payments, identities, and sensitive data while keeping the storefront fast.
It also means designing controls around real moments of risk: login, checkout, refunds, and admin changes.
That’s why security works best when it’s built into the full store setup from day one—see our complete guide to Ecommerce Website Development in the UAE.
The 3 security layers of an online store
A layered model keeps priorities clear and avoids over-securing low-risk areas while leaving high-risk areas exposed. Before you implement controls, define success in each layer: fewer successful attacks, fewer fraud losses, and faster recovery.
Secure checkout: payment flow design, gateway integration, and controls around card-related activity.
Customer data protection: personal information, order history, and account-data access controls.
Online store security / ecommerce cybersecurity: hosting, admin access, apps/plugins, APIs, monitoring, and incident response.
A secure online store improves all three layers, but the quickest return usually starts with checkout and admin identity.
PCI Compliance Ecommerce: The Practical View
PCI gets easier when you treat it as scope. The more your systems touch card details, the more requirements you inherit.
Many teams reduce PCI scope by using hosted payment pages or hosted fields so sensitive handling stays in the provider environment—an ecommerce security win.
Do I need PCI compliance ecommerce?
If you accept card payments, PCI applies in some form. The question is how large your scope is today. Identify your payment approach:
Redirect or hosted payment page: customers pay on the provider page; your exposure is typically lower.
Hosted fields / embedded components: the provider controls card entry.
On-site card entry: your site handles card input directly; requirements increase.
Card data storage: storing full card numbers or CVV is high-risk and should be avoided.
How to shrink scope without weakening checkout UX
Reducing scope is not doing less security.
It’s designing checkout so fewer parts of your stack can be used to steal payment data or manipulate orders. Before changes, set one rule: checkout edits must preserve speed and stability.
Use a reputable gateway with hosted pages or hosted fields.
Store tokens, not card numbers; never store CVV.
Limit who can change gateway settings and refund rules.
Log checkout configuration changes and credential updates.
Keep payment scripts minimal and vendor-supported.
For more on securing your payments, see our guide on Payment Gateways in the UAE.
Threats That Affect Ecommerce Most
Most incidents start with automation. Knowing what to defend first keeps ecommerce security focused on what causes loss.
What threats affect ecommerce most?
Attacker goals are consistent: steal accounts, test stolen cards, inject malicious code, or force refunds and chargebacks. Before choosing defenses, confirm you can observe these patterns.
Account takeover: hijacking customer accounts using leaked credentials.
Credential stuffing: high-volume automated login attempts.
Card testing: rapid checkout attempts to validate stolen cards.
Malware injection: scripts added to pages to skim or redirect.
Refund/returns abuse: friendly fraud and policy exploitation.
Admin compromise: weak passwords, missing MFA, shared accounts, excessive privileges.
If you cannot name the control and the signal you’ll monitor for each threat, your protection is incomplete.
How to Secure an Online Store: A 30-Day Plan
Security improves fastest when you ship in sequence. This 30-day plan reduces risk quickly and creates a baseline you can maintain.
Assign owners, validate outcomes, and record changes—this is ecommerce security as operations. Treat ecommerce security reviews like financial reviews: scheduled, owned, and documented.
Week 1: Baseline hardening
This week removes easy openings and stabilizes production. Before you start, make sure you have rollback and change tracking.
Enforce SSL and force HTTPS site-wide.
Patch your platform, themes, plugins/apps, and hosting components.
Remove unused extensions and abandoned integrations.
Reduce admin roles to least privilege; eliminate shared logins.
Turn on admin activity logs and configuration change tracking.
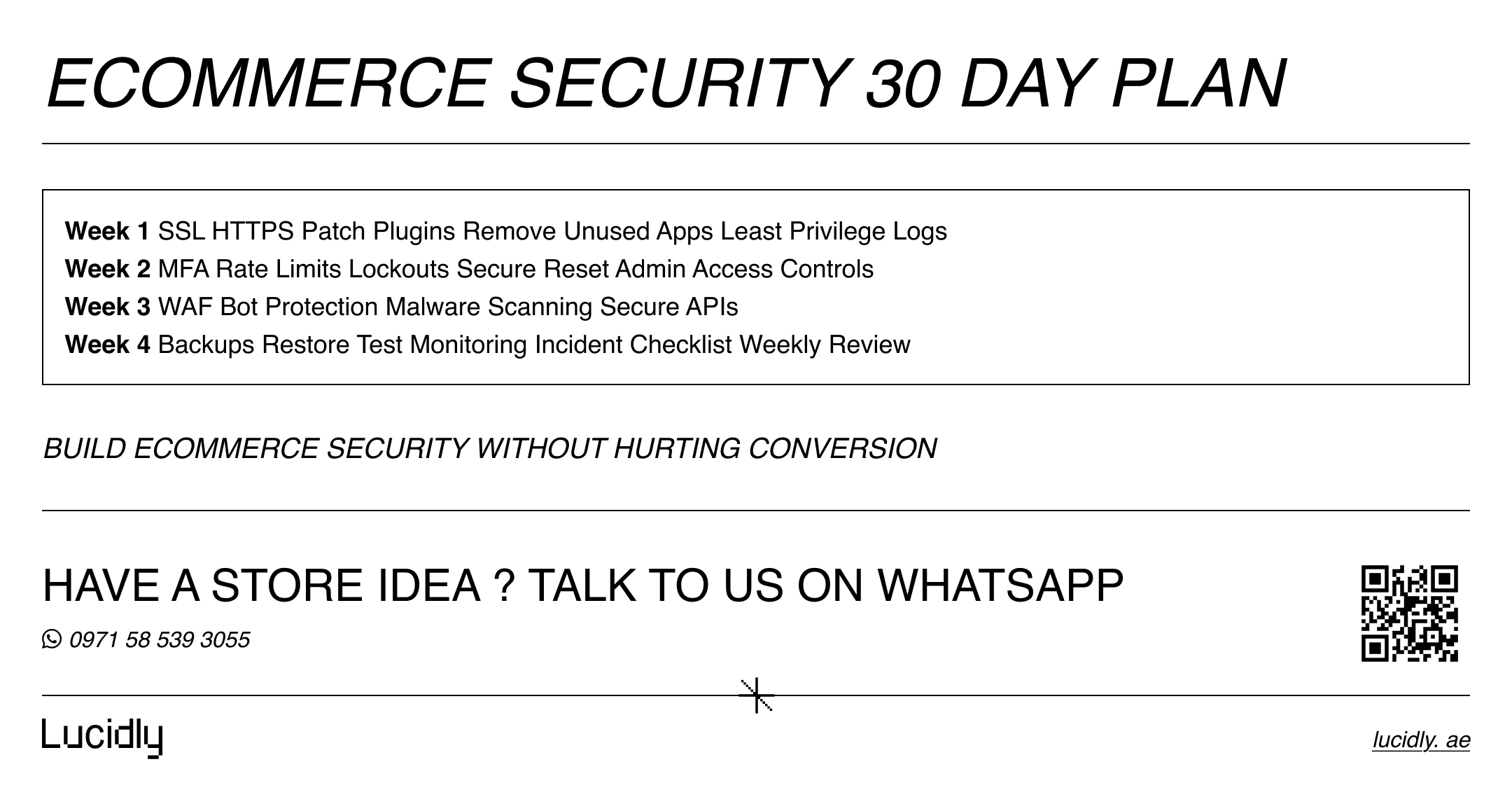
Week 2: Identity and access control
Identity is where many breaches begin. Protect roles that can change money-related settings first.
Enable MFA for admin and privileged support accounts.
Add rate limits and lockouts for repeated login failures.
Harden password reset flows (short expiry, verification, anomaly checks).
Restrict admin access paths where practical (IP allowlists or VPN).
Alert on unusual access events (new devices, new countries, odd patterns).
Week 3: Application and perimeter protection
This stage reduces bot damage and blocks common exploitation attempts. Define baseline traffic so you can tune rules safely.
Deploy a WAF with managed rules and bot mitigation.
Add rate limiting for login, checkout, and high-abuse endpoints.
Schedule malware scanning and alert on unauthorized file changes
Secure APIs with scoped tokens, validation, and strict permissions.
Disable debug configurations and remove exposed routes you don’t need.
Week 4: Resilience and recovery
Even strong stores face incidents; speed of detection and recovery matters.
Implement tested backups (daily + off-site) with restore drills.
Separate backup access from production credentials.
Add uptime and error monitoring with alerts.
Prepare a first-hour incident checklist (containment, credential rotation, validation).
Review weekly: new apps/scripts, admin additions, checkout changes.
Prevent Ecommerce Fraud and Reduce Chargebacks
Fraud control is about signal quality and decision consistency. Random blocks frustrate real customers; weak controls invite loss. The goal is risk-based friction: add steps only when signals indicate risk.
Mature ecommerce security treats fraud as a process you tune.
Where fraud enters the funnel
Fraud clusters at predictable points. Instrument these stages so you can catch patterns early. Before applying rules, define outcomes: allow, review, step-up, or block.
Account creation: bot signups and synthetic identities.
Login: credential stuffing and takeover attempts.
Checkout: card testing, mismatch signals, risky IPs and devices.
Post-purchase: chargebacks, refund abuse, returns manipulation.
Fraud rules you can deploy today
Start simple, then tune. You’re aiming for consistent decisions, not complexity.
Use fraud rules for velocity (many attempts/orders from one device, IP, or email).
Flag BIN/country mismatch and unusual shipping destinations.
Add step-up verification for high-risk orders (3DS where appropriate).
Block card testing patterns: rapid small payments, repeated declines, repeated CVV failures.
Set limits and alerts for unusual refund behavior and policy abuse.
Protect against account takeover
Account takeover creates the worst customer experience: stolen orders, changed addresses, and disputes.
Apply stronger checks only when risk signals appear.
Detect credential stuffing and add strict rate limits on login and reset endpoints.
Add confirmation steps for sensitive changes (email, address, phone).
Notify customers on high-risk events (new device login, password reset, profile changes).
Train support teams to resist social engineering during account recovery.
For a security-first ecommerce security setup, explore Lucidly’s Ecommerce Solutions in the UAE to secure checkout, reduce fraud risk, and strengthen customer data protection with PCI-aligned controls.
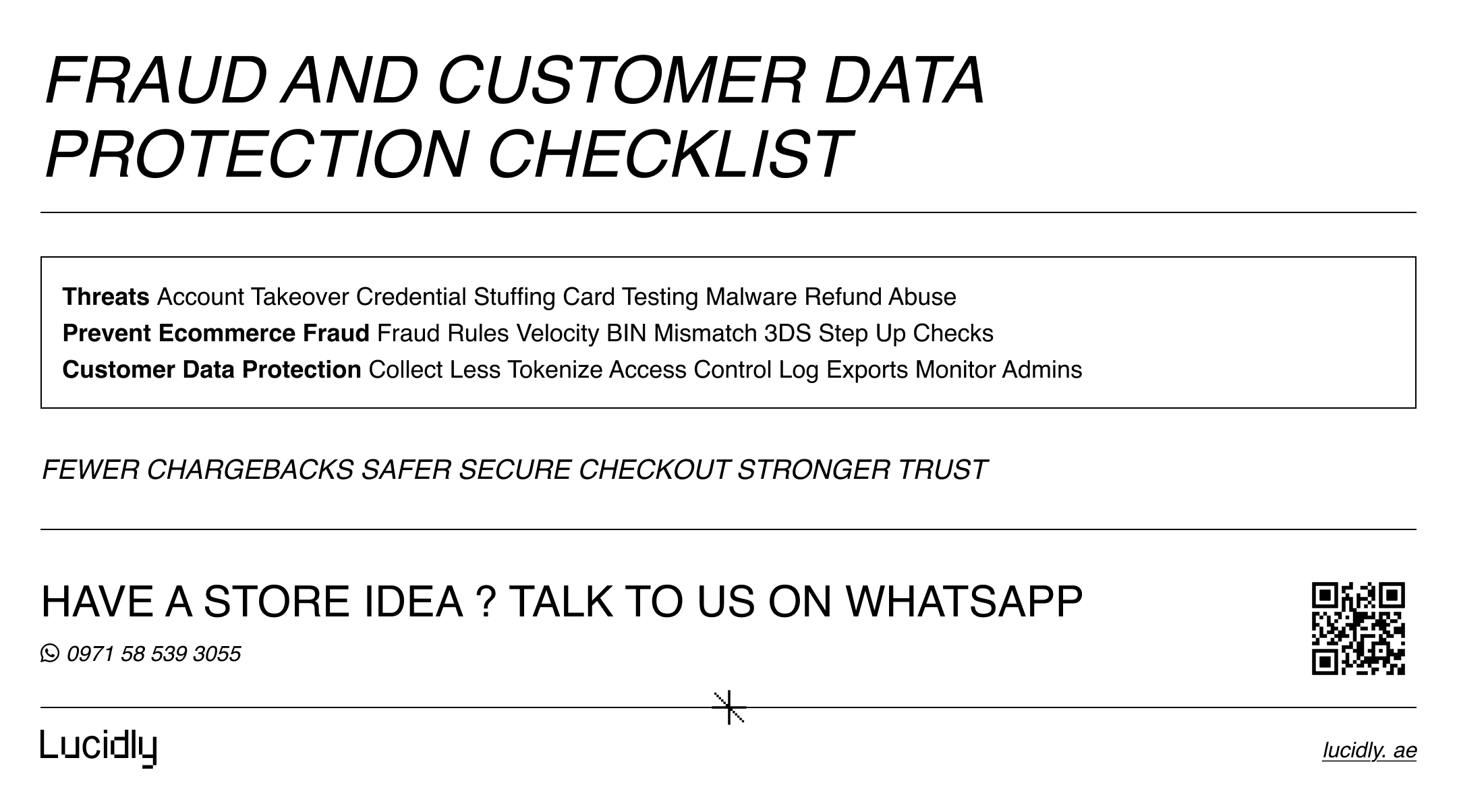
Customer Data Protection: Build It Into Operations
Data protection isn’t just encryption. Breaches often happen through privileged access, exports, or misconfigured tools.
Strong customer data protection limits what you store, who can access it, and how you detect misuse—an ecommerce security requirement for trust.
Minimize what you store
Minimization reduces risk immediately. Before changing retention, document what each data set is used for.
Avoid storing payment details; rely on gateway tokens.
Remove personal data from logs where possible.
Set retention windows for inactive accounts and abandoned carts.
Restrict and log customer exports and bulk downloads.
Secure access, encryption, and monitoring
Encryption helps, but access control prevents many incidents. Monitoring turns prevention into detection and response. Define which actions are sensitive and must be logged.
Encrypt data in transit and secure sensitive data at rest where supported.
Apply role-based access and least privilege across teams.
Log sensitive events: exports, refunds, address changes, role updates.
Alert on abnormal admin behavior and large-volume access patterns.
FAQ
Do I need PCI compliance?
If you accept card payments, PCI applies in some form. You can often reduce scope by using hosted payment pages or hosted fields so your systems don’t handle raw card details.
How do I protect customer data?
Use customer data protection basics: minimize collection, restrict access, log sensitive actions, encrypt where appropriate, and monitor privileged behavior and exports.
What threats affect ecommerce most?
Common threats include account takeover, credential stuffing, card testing, malware injection, refund abuse, and admin compromise. Automated attacks make monitoring and rate limiting essential.
How can I reduce fraud and chargebacks?
To prevent ecommerce fraud, deploy fraud rules (velocity and mismatch signals), add step-up verification for high-risk orders, harden login flows against account takeover, and build a consistent review process.
"To ensure ongoing protection of your store and reduce risk, it’s essential to integrate Ecommerce Maintenance and Support, including updates, monitoring, and continuous process improvements."
Security isn’t a cost center when it reduces refunds, chargebacks, and lost trust. Start by shrinking PCI scope, then ship the 30-day plan (SSL, MFA, WAF, backups, malware scanning).
Next, tune fraud rules and account takeover defenses using real signals. Done well, ecommerce security becomes a growth advantage: fewer incidents, a safer secure checkout, and stronger customer confidence at purchase.
Ready to strengthen your ecommerce security and protect checkout conversions? Message Lucidly on WhatsApp—or use the numbers on our Contact Us page to book a quick security audit.
References
PCI Security Standards Council (PCI SSC) — PCI DSS document library (official standards and guidance). (PCI Security Standards Council)
NIST — Special Publication 800-63 Digital Identity Guidelines (authentication and identity assurance guidance relevant to MFA). (NIST)
OWASP — Authentication Cheat Sheet (practical controls that help reduce credential stuffing and account takeover risk). (OWASP Cheat Sheet Series)
Cloudflare — Web Application Firewall documentation / overview (WAF concepts and rulesets). (developers.cloudflare.com)
